Resources
Nipper Resilience Use Case - Leveraging NE data in SIEM to report on the top exploited vulnerabilities identified by CISA
In August 2023, the Cybersecurity and Infrastructure Security Agency (CISA) released a joint Cybersecurity Advisory detailing the Common Vulnerabilities and Exposures (CVEs) exploited by malicious cyber actors in 2022 and the associated Common Weakness Enumerations (CWE).
It was noted that these malicious cyber actors targeted older software vulnerabilities at a higher frequency than more recently disclosed vulnerabilities.
Unpatched, internet-facing systems were some of the most common targets. A finding which CISA has already acted on by issuing a binding directive to federal agencies ordering them to disconnect networked management devices from the internet.
For devices that cannot be removed from the internet, CISA and other agencies are urging organizations, as well as vendors, designers, and developers, to implement mitigating measures to reduce the risk of compromise.
Organizations must be able to identify and report on which CVEs their network is exposed to (currently and historically) to carry out effective mitigation and remediation. Achieving this on an enterprise scale network presents numerous challenges.
Titania has been working with customers to overcome the challenge of insufficient resources as they secure and assure their increasingly complex networks. Our network assurance solution Nipper Resilience, continuously assesses the security risk posture of every router, switch, and firewall in the network on an up-to-hourly basis, identifying and reporting on any known vulnerabilities and configuration changes.
Among the top routinely exploited vulnerabilities identified in the advisory are those directly and indirectly linked to networking devices
The advisory identifies two exploitable vulnerabilities directly linked to networking devices. The first, CVE-2018-13379, is a path traversal vulnerability and affects certain versions of FortiOS which run on Fortinet networking devices. Initially discovered by researchers in August 2019, this exploit attempt was detected in the wild less than a month later. The exploitation allows an attacker to read the ‘sslvpn_websession’ file containing username and plaintext password data on a vulnerable system.
The other, CVE-2022-1388, is a missing authentication vulnerability, affecting certain versions of F5 BIG IP. This vulnerability can allow attackers with network access to BIG-IP through the management port or self IP addresses to execute arbitrary system commands, create and delete files and disable services.
Following reports of exploitation in both government and private sector networks, CISA released an advisory last year that urged administrators to upgrade their software to fixed versions.
These CVEs, left undetected and therefore unmitigated, could have disastrous consequences, allowing malicious attackers to either access confidential data in the network or take control of systems.
Another feature on the list was the infamous Log4j2 vulnerability, an event that highlighted fundamental gaps in the adoption of vulnerability detection and response practices in both the public and private sectors.
Discovered in 2021, the vulnerability was soon publicly disclosed, prompting a race to find and patch the issue before threat actors moved in. Unfortunately, the flaw was already present in hundreds of major enterprise products, including networking devices.
Cisco was just one affected vendor with vulnerable products including its Firepower Threat Defense and enterprise routing and switching systems Cisco Network Assurance Engine and Cisco SD-WAN vManage.
Despite widespread response from vendors with software updates, threat actors continue to find vulnerable applications. Reports suggest that almost a quarter of Log4j downloads everyday are vulnerable versions of the library.
This indicates the number of organizations not minimizing their attack surface effectively. Failure to identify and mitigate such vulnerabilities make these organizations highly susceptible to attacks and presents a high level of risk to the confidentiality, integrity and availability of systems and data in the network.

Research conducted on behalf of Titania looked at current approaches to mitigating the risks of exploitable misconfigurations in network security. The results show organizations are prioritizing firewall security and report a fast time to respond to misconfigurations when detected in annual audit. However, switches and routers are only included in 4% of audits and these devices play a vital role in reducing an organization’s attack surface and preventing lateral movement across the network.
The advisory recommends end-user organizations continuously monitor the attack surface and implement ZTNA
CISA and other agencies have set out a list of recommended mitigation measures for both vendors and developers and end-user organizations. The focus for organizations is on improving their cybersecurity posture and aligning with NIST recommended practices.
For example, routinely performing automated asset discovery to identify and catalogue all systems, services, hardware and software is advised. As is documenting secure baseline configurations and all deviations from the initial secure baseline.
Protective controls and architecture measures are also a focus of the advisory. The implementation of Zero Trust Network Architecture (ZTNA) is a critical step. The US Department of Defense has already set out its Zero Trust strategic goals and timeline for execution.
ZTNA should limit or block lateral movement by controlling access to applications, devices, and databases. The approach precludes default trust of any user, network, system or service operating within or outside of the security perimeter. It uses a data centric approach to continuously verify every user, device and application.
“A determined attacker will try a combination of approaches to access a network until they gain entry, and known vulnerabilities or misconfigurations are an easy way in. Companies must adopt both a zero trust mindset and network security best practices, to minimize the attack surface, inhibit lateral movement, and prevent intruders from meeting their goals.” - Phil Lewis, Senior Vice President
Continuous monitoring of the attack surface is another preventative action organizations must take to enable them to identify and investigate abnormal activity that may indicate cyber actor or malware lateral movement. Continuous monitoring at enterprise level requires the use of scalable automation tools.
Using Nipper Resilience to continuously monitor networks for CVEs
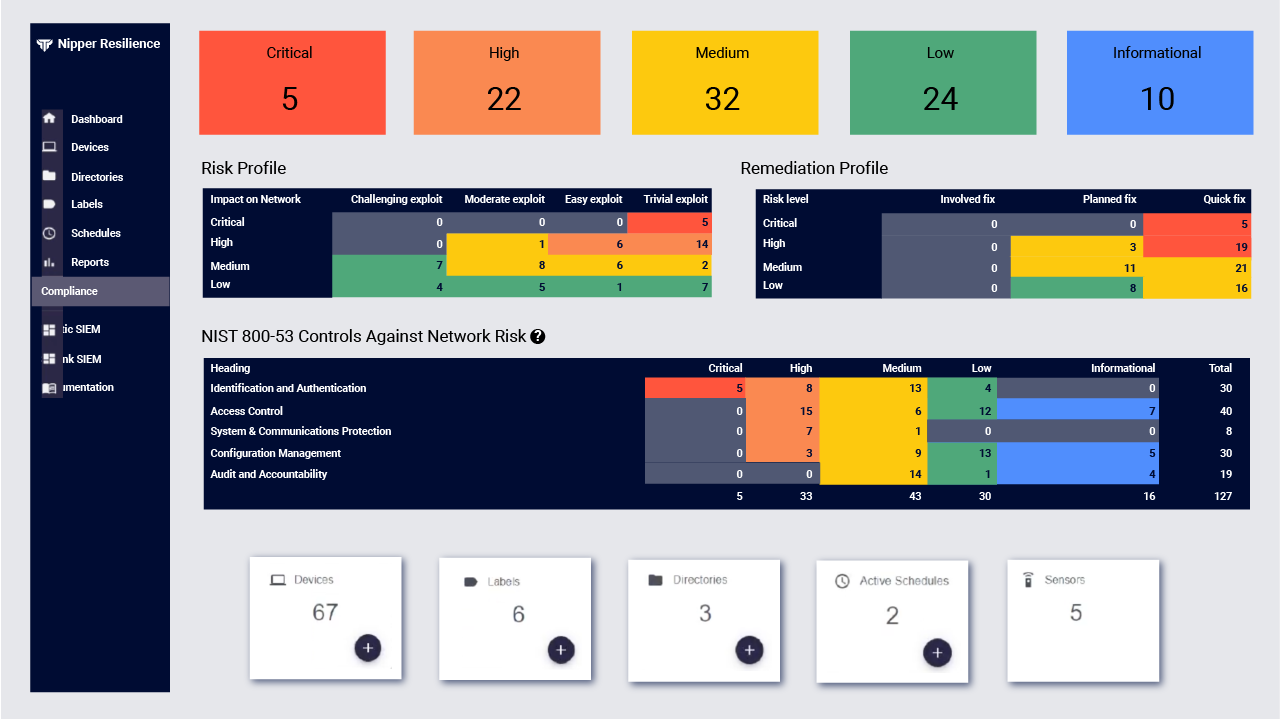
Nipper Resilience accurately assesses the security risk posture of up to > 250k switches, routers and firewalls per audit – and proactively thereafter to continuously monitor security and compliance. Findings are prioritized by risk criticality – based on network segment, industry specific attack vectors, ease of exploitation, and impact – and are reported with device specific remediation advice to improve MTTR. The solution provides Rest APIs and JSON outputs for integration with trusted 2FA, SIEM, SOAR, GRC and trouble-ticketing solutions.
How can Nipper Resilience be used to report on the top exploited vulnerabilities identified in the advisory?
Nipper Resilience pushes granular vulnerability findings data to SIEM(s). For a given CVE, such as CVE-2018-13379, it allows you to, very quickly, query which network devices in any given network segment across the network were exposed to this vulnerability at a particular point in time. Allowing you to forensically assess your exposure and risk historically as well as the current state of play.
With MITRE ATT&CK and MITRE CAPEC data available too, you can also very quickly assess your current and historic exposure to Tactics and Techniques being used in the wild. Giving you visibility of vulnerabilities and misconfigurations through an attacker’s lens, to better understand your attack surface exposure.
Nipper Resilience can help implement a Zero Trust approach
Our solution delivers continuous assessment of all networked routers, switches and firewalls as advocated for in a Zero Trust approach. Visit our product page to find out more or request a Proof of Concept from the team.