Latest news
An update on the Apache Log4j vulnerability and Nipper

Following the announcement of the Apache Log4j vulnerability, Titania has investigated and would like to confirm that neither Nipper nor Nipper Resilience are susceptible to this vulnerability as they do not use the affected log4j Java library.
However, as part of best practice we always recommend that you always use the latest version of Nipper. The current version is 2.12.1 and can be downloaded in your account area.
If you would like to learn more about this vulnerability, see the links below for further information.
- https://nvd.nist.gov/vuln/detail/CVE-2021-44228
- https://www.ncsc.gov.uk/news/apache-log4j-vulnerability
Using Nipper to check your devices for Log4j vulnerability
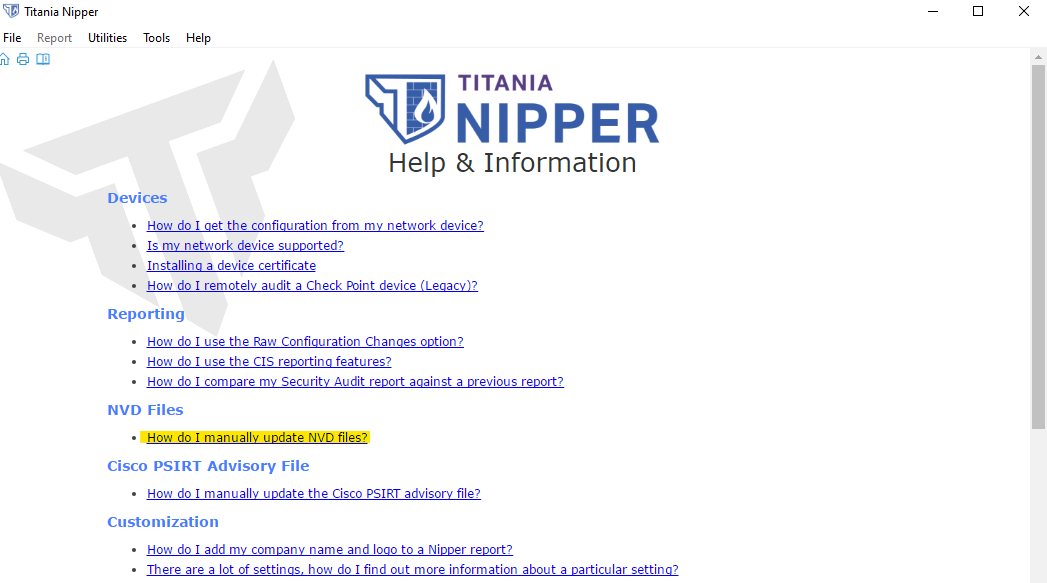
Nipper can be used to check if any supported devices are affected by this vulnerability. As this vulnerability has been published since our last product update, in order to do this you will have to manually update the resources (i.e. NVD CVE's) within Nipper. Instructions to manually update the resources can be found in Nipper’s Help & Information section on the Home screen within the tool. Once you have updated the resources, the Vulnerability Audits run from Nipper will now include checks for the Log4j vulnerability.