Resources
CVSS – what it is and how it works
The Common Vulnerability Scoring System is a free and open-source industry standard for assessing the severity of computer system vulnerabilities. By attempting to assign a severity score to a vulnerability, it allows those responsible for rectifying the issues to prioritize their responses and resources according to the threat level. It assigns a score of between 0 and 10 to each vulnerability, where 10 reflects the most severe threats. The assignment is made based on the severity of the threat and the impact it could have if exploited.
There are three different metric groups for the CVSS score, a base score plus environmental (metrics based on the environment the vulnerability is found in) and temporal (metrics reflecting how the vulnerability changes over time) scores which provide context for the base score.
The CVSS is referenced in risk management frameworks as a method of understanding the vulnerability of an impact, for example in NIST 800-53, specifically in the discussion for RA-5, vulnerability monitoring and scanning, where it speaks to ‘Organizations also consider using scanning tools that express vulnerability impact by the Common Vulnerability Scoring System (CVSS).’
But there are issues with the CVSS especially when considering configuration vulnerabilities rather than software vulnerabilities. One of the key issues when using this scoring system to audit firewalls, switches and routers for configuration vulnerabilities, is that it makes the assessments of vulnerability predominantly on the device in isolation and does not always consider the ramifications on the wider network in a nuanced enough way. This could mean that a severe risk to the network is not identified, or time and effort is spent rectifying a vulnerability which has little to no impact on the network rather than those which are key to its security.
Nipper’s Security Audit - what’s different to CVSS?
The CVSS assesses the severity of software vulnerabilities for individual devices. However, to accurately determine the severity of a risk posed by a misconfiguration (which will persist through patching) a different assessment and scoring system is needed.
To understand the risk posed by configuration vulnerabilities in networking devices, it is necessary to analyse the configuration in the context of the entire network if the identified vulnerabilities are exploited. Which is why Nipper assesses, scores and prioritizes configuration vulnerabilities in routers, switches and firewalls by providing a network risk context for every issue it finds.
By virtually modelling the entire configuration as a single entity, Nipper’s analysis considers the interdependencies of the configuration settings and suppresses findings that are irrelevant, for example, because they are not enabled elsewhere in the configuration. The same is true for complex configurations within firewall devices, where intricate filter rules can cause security issues, and all of the rules must be ingested and analyzed simultaneously to discover them. Some products use CVSS severity rather than risk scoring, but Nipper also takes into account other factors representing risk to the network, not just to the device. This includes:
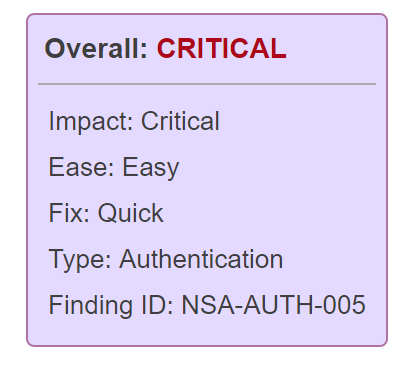
- The impact of an exploitation of the misconfiguration (to both the device and the network)
- How easy it is to exploit it, i.e.to assess risk likelihood
- How easy it is to remediate.
The Nipper security report then automatically prioritizes the risks identified by criticality to the network. This provides security teams with insight into what to fix first. As a result, Nipper is proven to reduce security team’s mean time to detect (MTTD) misconfigurations and vulnerabilities, as well as equipping network teams to reduce the mean time to remediate (MTTR) known security gaps.
Practical example of Risk Prioritization from Nipper
A practical example of how Nipper’s risk prioritization works for a firewall is the check for network filtering. As part of its security audit, Nipper checks if network filtering is enabled. The CVSS v3 score for this vulnerability is 5.0 (Medium), if all environmental metrics are set to ‘High’ i.e. this is an important system, where if it’s exploited it would have the highest possible impact.
The fact that filtering is not enabled doesn’t have much of an impact on the device with regards to it’s potential to compromise the confidentiality, integrity and availability of systems, applications or data. In the example of a firewall, the fact that traffic is allowed to flow through the system does not affect the device. It doesn’t mean that an attacker can log onto the device and change things.
However, the fact that all and any traffic is being allowed through could have a catastrophic effect on the network and the systems that the firewall is supposed to be defending, which is why Nipper gives this vulnerability a ‘Critical’ rating.
Run Nipper’s security audit to identify and assess the severity of the misconfiguration risks on your network: