Network Infrastructure Security Automation
Introducing Nipper Solutions
Whether you’re looking for network resilience assurance based on your industry-specific attack vectors, or a way to accurately report network/device-level security and compliance posture – even in air-gapped environments - there’s a Nipper solution for you.
Which Nipper solution is right for you?
Titania specializes in scaling Network Security automation software for network infrastructure – routers, switches and firewalls – and helping organizations determine their most critical risks for remediation, before they are exploited.
Our roadmap is dedicated to the devices, environments, risk management frameworks, and regulatory challenges you care about. ‘Better Together’, we work with your technology providers and device manufacturers, to architect solutions that drive more value from your security tech-stack.
The right solution for your organization will depend on the size of the network you need to analyze, and where you are on the journey to network readiness, recoverability and resilience.
Continuous Network Exposure Risk Management
Scalable Security & Compliance Posture Management
CMDB-centric Configuration Management
Accurate Device Vulnerability Assessments
Ready for next-gen, real-time Network Exposure
risk management,
at scale?
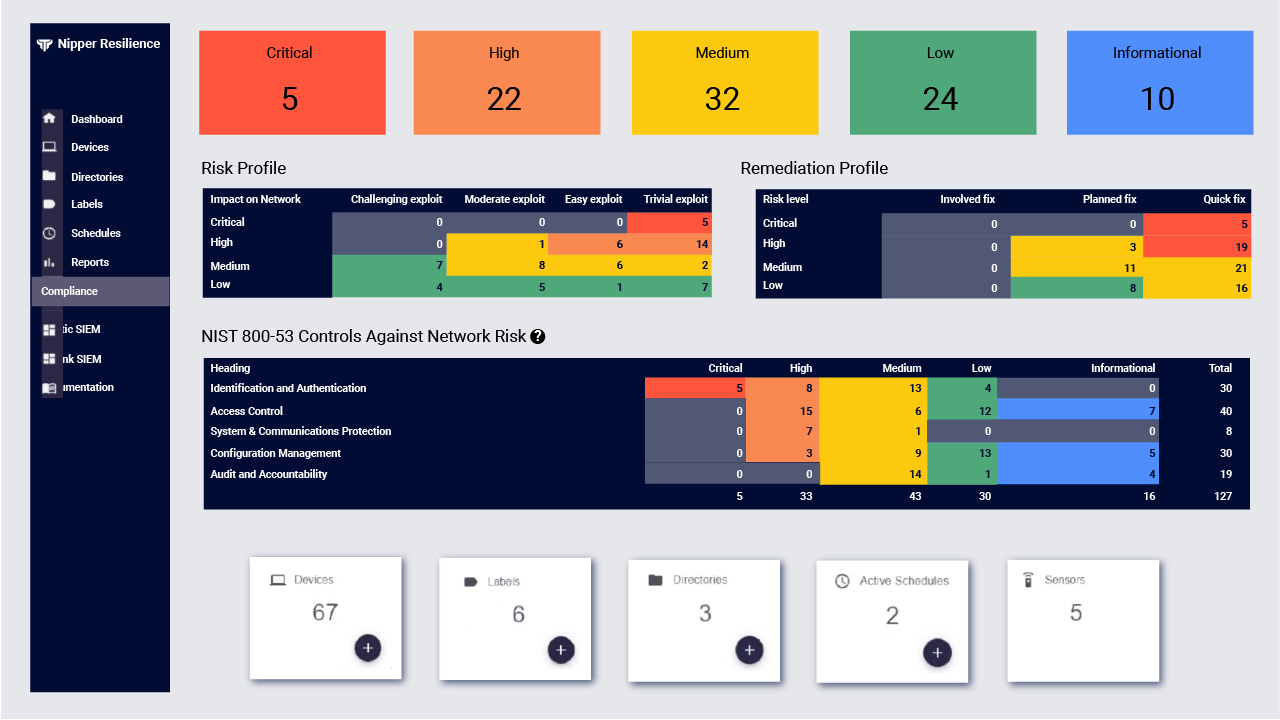
Protect networks from threats and disruptions with Nipper Resilience, designed to enable organizations to proactively:
- Enforce network segmentation to minimize attack surface and contain threats
- Gain full network visibility to detect potential indicators of compromise
- Assess exposure to industry-specific attack vectors and mitigate operational risks
- Maintain accurate CMDBs to support rapid recovery and business continuity
NOCs, SOCs, Incident Response & Remediation teams
Nipper Resilience is deployed by SOCs that need real-time, network exposure management to get ahead of industry-specific threats. Valuable to Incident Response and Remediation teams, the findings prioritize and inform investigations and shut-down attacks. Whilst NOCs benefit from a next-gen configuration management to recover from and prevent network disruptions.
Need accurate, on-demand Device Vulnerability Assessments for routers, switches and firewalls?

Automatically assess whether configurations adhere to vendor hardening guides, mandated industry regulations and security benchmarks, with:
- Drill-down to details of specific tests run on the configuration
- Impact analysis if vulnerability is exploited, ease of exploit, and ease of fix
- Risk-prioritized view of non-compliances and security check failures
- Remediation analysis to improve compliance posture and MTTR
- Evidence-based, assessor-ready compliance reports
Internal and External Security Teams, Compliance Auditors & Pentesters
Nipper significantly reduces the time spent auditing routers, switches and firewalls against security controls and RMFs with advanced network contextualization analysis that suppresses irrelevant findings, prioritizes risks by criticality, and automates device-specific guidance on how to fix misconfigurations. Nipper’s high-fidelity reports can be white-labelled for your branding.
CISA Director, on the importance of network infrastructure:
"Routers and firewalls and switches - which would likely never be part of a systemically important entities list - are the connective tissue and the soft underbelly [of critical infrastructure] for our adversaries."
“Nipper plays an important role as it helps to audit every device accurately and enables us to dedicate our valuable resources by analyzing and prioritizing fixes.”
Senior Analyst, Retail

“It provides best services in its class by discovering vulnerability in routers, switches and firewalls and automatically prioritizes risks to organization. Its virtual modelling is one of the best features that provides exact fixes by reducing false positives and helps us to be secure and compliant.”
IT Services Industry

“We have been using Nipper for many years now in our business unit and we find the product very useful in maintaining our regulatory and contractual requirements. We are using Nipper for our network devices which enables us to identify non-compliance in our network devices configurations.”
Information Security Operations, IBM

“What I love about Nipper, especially when it comes to PCI, is that it gives you recommendation distinctions where it says ‘here are the areas where you might want to look’. That’s how we found out that local account passwords in our routers weren’t adequate.”
Security Risk Management, Telecommunications

“The biggest advantage I find with Nipper is the speed of response… in terms of speed of getting results and getting a quick overview it’s fantastic. There’s nothing else like it out there as far as we’re aware.”
International Logistics Facility


Why Titania Solutions?
At the forefront of proactive network security, Titania solutions are trusted by NOC, SOC, Incident Response and cybersecurity teams to safeguard critical infrastructure, their supply chains, and critical commercial entities, globally.
We work with carefully selected resellers, supply chain partners, and prime contractors around the globe to ensure Titania software is implemented, integrated, and supported in-country.